The Universal Middleware (UMW) is the foundational software layer that enables SmartCMS, UKC, and all Bit4id applications to interact seamlessly with smart cards, USB tokens, PKCS#11 devices, and operating‑system‑level cryptographic APIs.
UMW provides a unified, multi‑platform, vendor‑agnostic abstraction for cryptographic tokens, ensuring maximum compatibility and stability across all supported systems.
UMW includes:
- PKCS#11 cryptographic library
- Microsoft CSP/KSP modules
- CryptoTokenKit support for macOS
- Smart card drivers
- Certificate store integration
- A pluggable cryptographic engine
- PC/SC or PCSC‑Lite communication layers
- Unified engine used by both UKC and SmartCMS
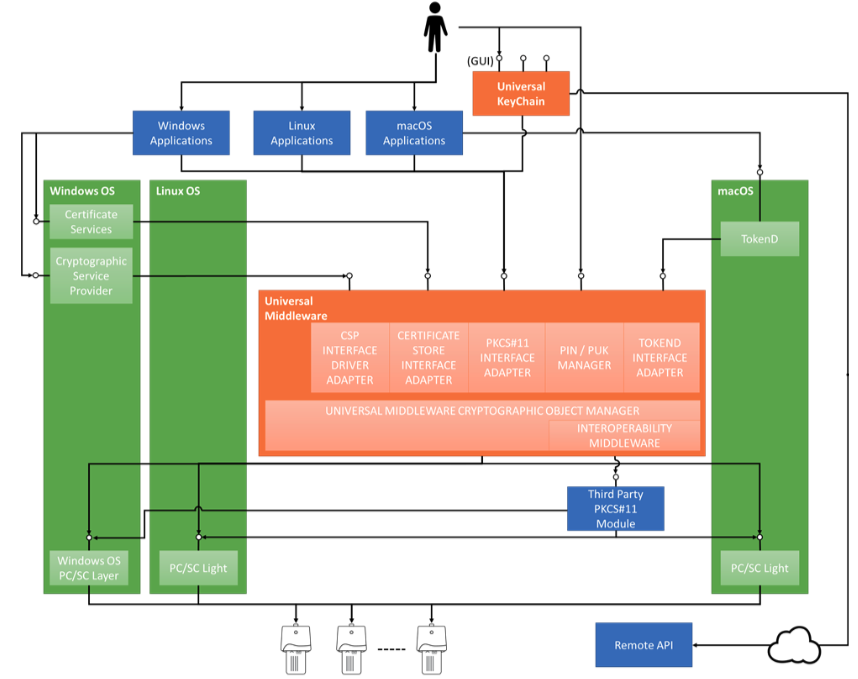
The UMW is composed of several subsystems that sit between:
- Applications
- Operating system cryptographic APIs
- Smart cards / PKI tokens
This abstraction allows applications to use smart cards without requiring vendor‑specific drivers or SDKs.
All smart card operations — signature, authentication, certificate retrieval, key management — are executed transparently.
Key architectural layers include:
- PKCS#11 library: Interface for applications that need low‑level cryptographic access
- CSP/KSP (Windows): Integration with Microsoft CryptoAPI
- CryptoTokenKit (macOS): Native smart card integration for macOS
- Engine Core: Manages security objects inside the smart card
- Plugin System: Extends engine support to multiple card families
- Certificate Store Extension (Windows): Allows reading smart card certificates directly into the OS certificate store
The architecture allows third‑party applications (Adobe Acrobat, Microsoft Office, Mozilla Firefox, VPN clients, etc.) to access smart card certificates with no additional configuration.
UMW supports major international smart card manufacturers, including:
- Gemalto
- Giesecke & Devrient (G&D)
- Siemens
- Oberthur
- ST Incard
- Additional cards integrated via plugin mechanism
The system is designed for extensibility: new cards can be integrated easily by adding a new plugin without modifying the core engine.
UMW is fully compatible with:
- Windows 10 / 11
- macOS 12 – 13
- Linux (Ubuntu 22.04 LTS)
All communication with smart cards follows the PC/SC standard:
- On Windows → Microsoft PC/SC
- On Linux/macOS → PCSC‑Lite
UMW acts as the bridge between the cryptographic APIs of each OS and the physical or virtual devices.
UMW exposes all required cryptographic operations used by PKI‑based systems:
- RSA (no limitation imposed by middleware; dependent on smart card capabilities)
- SHA‑1, SHA‑256, SHA‑384, SHA‑512
- Secure digest and signing operations
- On‑card key generation (when supported)
UMW allows:
- Secure key usage on smart cards
- Access to authentication and signature certificates
- Management of certificate objects
- Loading certificates into OS stores (Windows)
These operations are accessible transparently to any compliant application.
The PKCS#11 library is one of the most important UMW components.
It provides:
- Access to private keys stored on tokens
- Standardized interfaces for cryptographic operations
- Compatibility with:
- Mozilla Firefox
- Thunderbird
- Java applications
- PDF signing software
- VPN clients
- Cryptographic libraries requiring PKCS#11
- SmartCMS personalization workflows
PKCS#11 is also used by SmartCMS during:
- Token personalization
- Certificate enrollment
- Batch production
- Self‑service card initialization
On Windows systems, UMW includes a Microsoft Cryptographic Service Provider (CSP) and Key Storage Provider (KSP).
The CSP/KSP layer:
- Allows the smart card to appear as a cryptographic provider to Windows
- Supports Windows Logon with smart cards
- Enables signature in Microsoft Office (Word, Outlook, Excel)
- Integrates with Windows Certificate Store
- Enables TLS/SSL authentication in browsers using OS cryptographic APIs
Thanks to this integration, users can sign or authenticate using their smart card without needing separate drivers.
For macOS, UMW provides native support through CryptoTokenKit, enabling:
- Smart card discovery
- Certificate browsing
- PIN management
- Secure signature operations
- Integration with macOS applications such as Safari and Mail
This ensures a consistent user experience comparable to Windows environments.
UMW may optionally extend the Windows certificate store by automatically importing smart card certificates into:
- “MY” (personal) store
- Other logical stores when configured
Automatic import
Certificates are visible even after card removal.Synchronized mode
Certificates appear when the card is inserted and disappear when removed.
This avoids certificate clutter and improves usability.
UMW uses a modular plugin system to support different card technologies.
Plugins:
- Extend the core engine with card‑specific logic
- Are loaded dynamically
- Can be added or replaced without recompiling the whole system
- Provide compatibility with a wide range of smart cards and tokens
This architecture ensures long‑term maintainability and easy system evolution.
Communication between UMW and smart cards is managed by the PC/SC interface.
UMW:
- Sends APDU commands to smart cards
- Handles card/reader events
- Detects card insertion/removal
- Manages secure PIN entry
- Interfaces with personalization printers and hardware used by SmartCMS batch station
This low‑level engine ensures high reliability during operations like:
- Electronic personalization
- On-card key generation
- Certificate import
- PIN update/reset
- Reading card metadata
UMW is used by:
SmartCMS personalization workflows, for:
- Smart card initialization
- Key generation
- Certificate download
- Device verification
Batch Station, for:
- Large‑scale card/token production
- Industrial issuance campaigns
Universal KeyChain (UKC), for:
- Certificate browsing
- Local and remote signing
- Authentication to remote tokens and identity servers
UMW is therefore a core middleware layer underpinning the entire SmartCMS platform.
Without UMW, none of the token operations would be possible across multiple OS environments.
The Bit4id Universal Middleware (UMW) provides:
- A cross‑platform, standardized system for interacting with smart cards
- Support for all major card brands
- PKCS#11, CSP/KSP, and CryptoTokenKit interfaces
- Secure key usage and certificate operations
- Plugin‑based extensibility
- Integration with SmartCMS, Batch Station, and UKC
- PC/SC communication and driver abstraction
- Multi‑platform portability (Windows, macOS, Linux)
Thanks to this architecture, SmartCMS can work in heterogeneous environments and support a wide range of devices and identity profiles with maximum compatibility and security.